
Ron Amadeo
It seems firms that stonewall the media’s safety questions really aren’t good at safety. Final Tuesday, Nothing Chats—a chat app from Android producer “Nothing” and upstart app firm Sunbird—overtly claimed to have the ability to hack into Apple’s iMessage protocol and provides Android customers blue bubbles. We instantly flagged Sunbird as an organization that had been making empty guarantees for nearly a 12 months and appeared negligent about safety. The app launched Friday anyway and was instantly ripped to shreds by the Web for a lot of safety points. It did not final 24 hours earlier than Nothing pulled the app from the Play Retailer Saturday morning. The Sunbird app, which Nothing Chat is only a reskin of, has additionally been put “on pause.”
The preliminary gross sales pitch for this app—that it might log you into iMessage on Android when you handed over your Apple username and password—was an enormous safety pink flag that meant Sunbird would want an ultra-secure infrastructure to keep away from catastrophe. As an alternative, the app turned out to be about as unsecure as you possibly can probably be. Here is Nothing’s assertion:
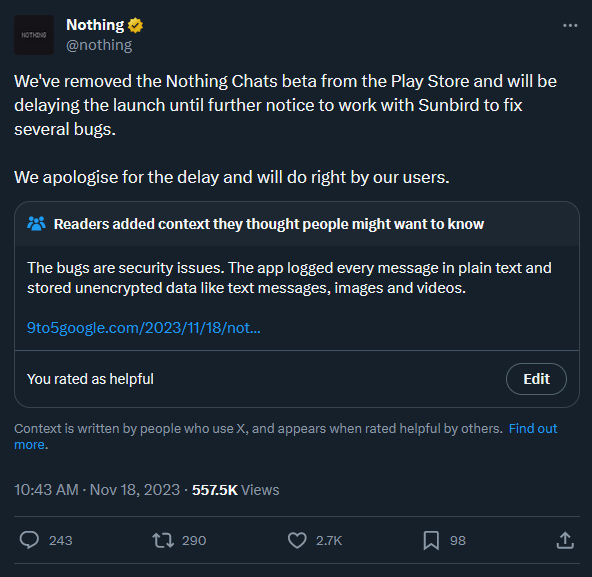
Nothing Chat’s shut down put up.
How unhealthy are the safety points? Each 9to5Google and Textual content.com (which is owned by Automattic, the corporate behind WordPress) uncovered shockingly unhealthy safety practices. Not solely was the app not end-to-end encrypted, as claimed quite a few occasions by Nothing and Sunbird, however Sunbird really logged and saved messages in plain textual content on each the error reporting software program Sentry and in a Firebase retailer. Authentication tokens have been despatched over unencrypted HTTP so this token might be intercepted and used to learn your messages.
The Textual content.com investigation uncovered a pile of vulnerabilities. The weblog says, “When a message or an attachment is acquired by a person, they’re unencrypted on the server facet till the consumer sends a request acknowledging, and deleting them from the database. Which means an attacker subscribed to the Firebase Realtime DB will at all times have the ability to entry the messages earlier than or in the intervening time they’re learn by the person.” Textual content.com was capable of intercept an authentication token despatched over unencrypted HTTP and subscribe to modifications occurring to the database. This meant stay updates of “Messages in, out, account modifications, and so forth” not simply from themselves, however different customers, too.
Textual content.com launched a proof-of-concept app that might fetch your supposedly end-to-end encrypted messages from Sunbird’s servers. Batuhan Içöz, a product engineer for Textual content.com, additionally launched a device that may delete a few of your information from Sunbird’s servers. Içöz reccomends that any Sunbird/Nothing Chat customers change their Apple IDs now, revoke Sunbird’s session, and “Assume your information is already compromised.”
9to5Google’s Dylan Roussel investigated the app and located that, along with the entire public textual content information, “The entire paperwork (photos, movies, audios, pdfs, vCards…) despatched via Nothing Chat AND Sunbird are public.” Roussel discovered 630,000 media recordsdata are at present saved by Sunbird, and apparently he might entry some. Sunbird’s app urged that customers switch vCards—digital enterprise playing cards filled with contact information—and Roussel says the non-public info of two,300-plus customers are accessible. Roussel calls the entire fiasco “in all probability the most important “privateness nightmare” I’ve seen by a telephone producer in years.”